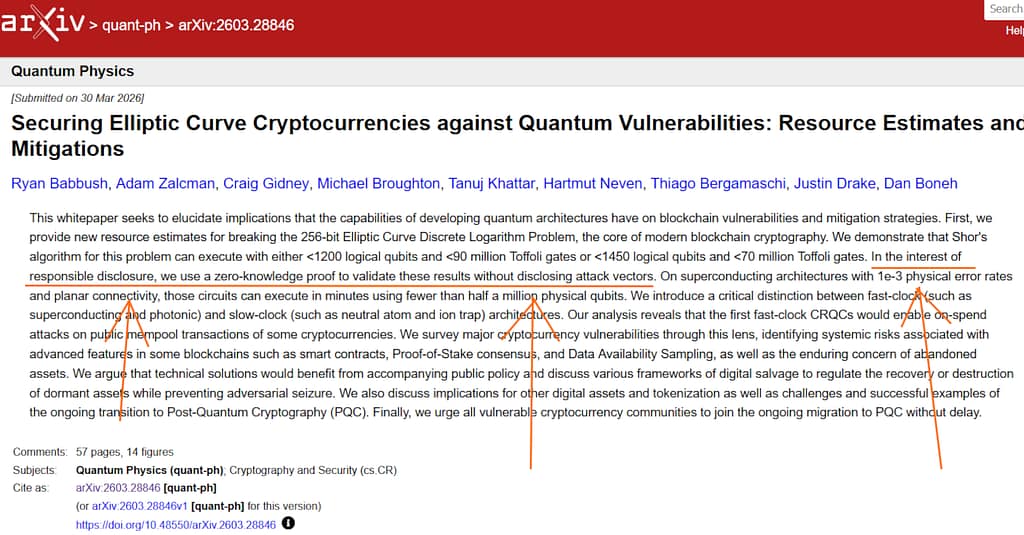
The Quiet Exit: How a Private Lab May Have Already Broken Blockchain Cryptography — and Why You…
The Quiet Exit: How a Private Lab May Have Already Broken Blockchain Cryptography — and Why You Won’t Find It in the Literature Author: Berend Watchus. Publication for OSINT Team. April 1, 2026 Published today on arxiv.org by combined team: Google Quantum AI, Santa Barbara, CA 93111, United States2Department of Computer Science, University of California Berkeley, Berkeley, CA … Read more