How a Public Anon Key Led to Full Database Compromise
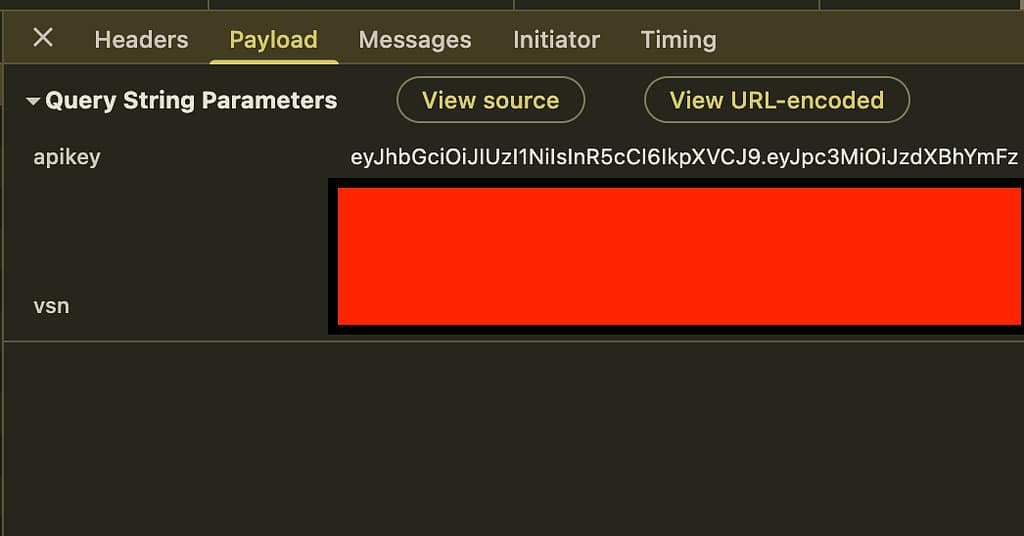
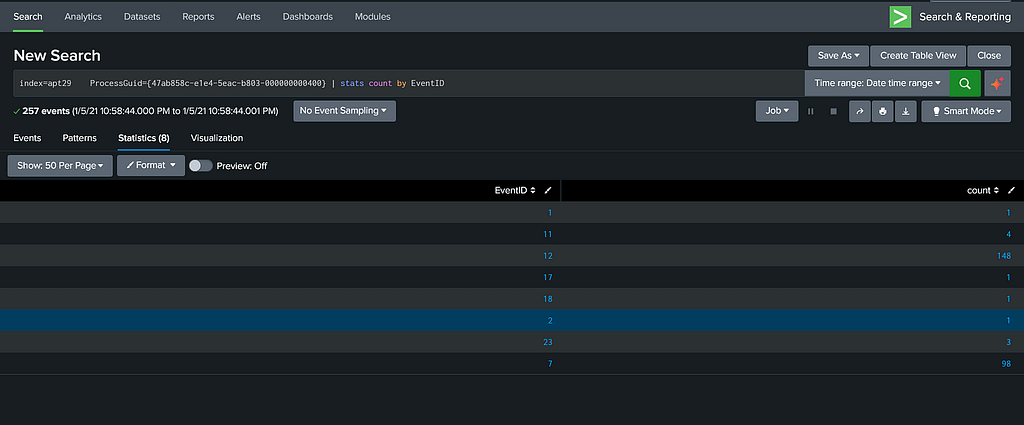
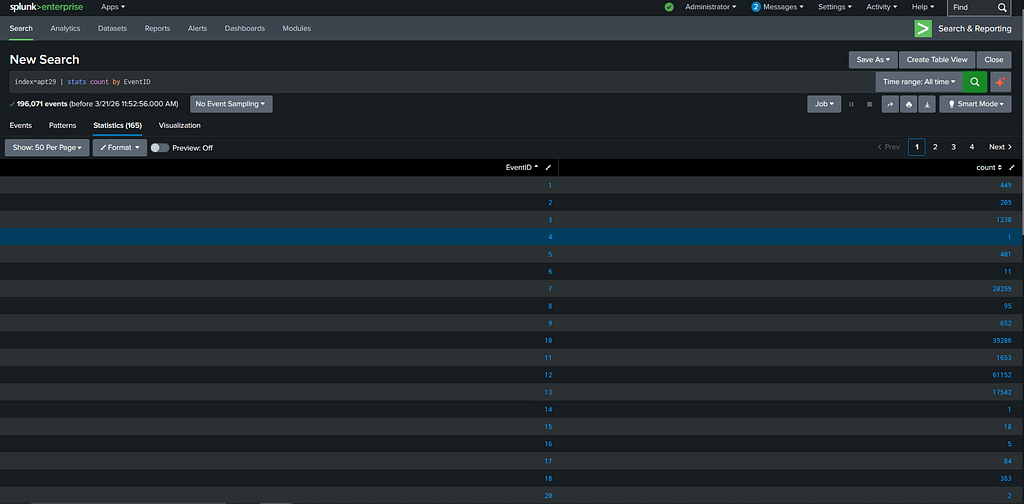
In March 2026, I conducted a penetration test against a social media-style web application (referred to as TargetApp.io). The engagement was authorized by the platform’s owner and spanned approximately two weeks. The most critical vulnerability was discovered on the second day. While the test began as a traditional black-box assessment, simulating an external attacker with … Read more