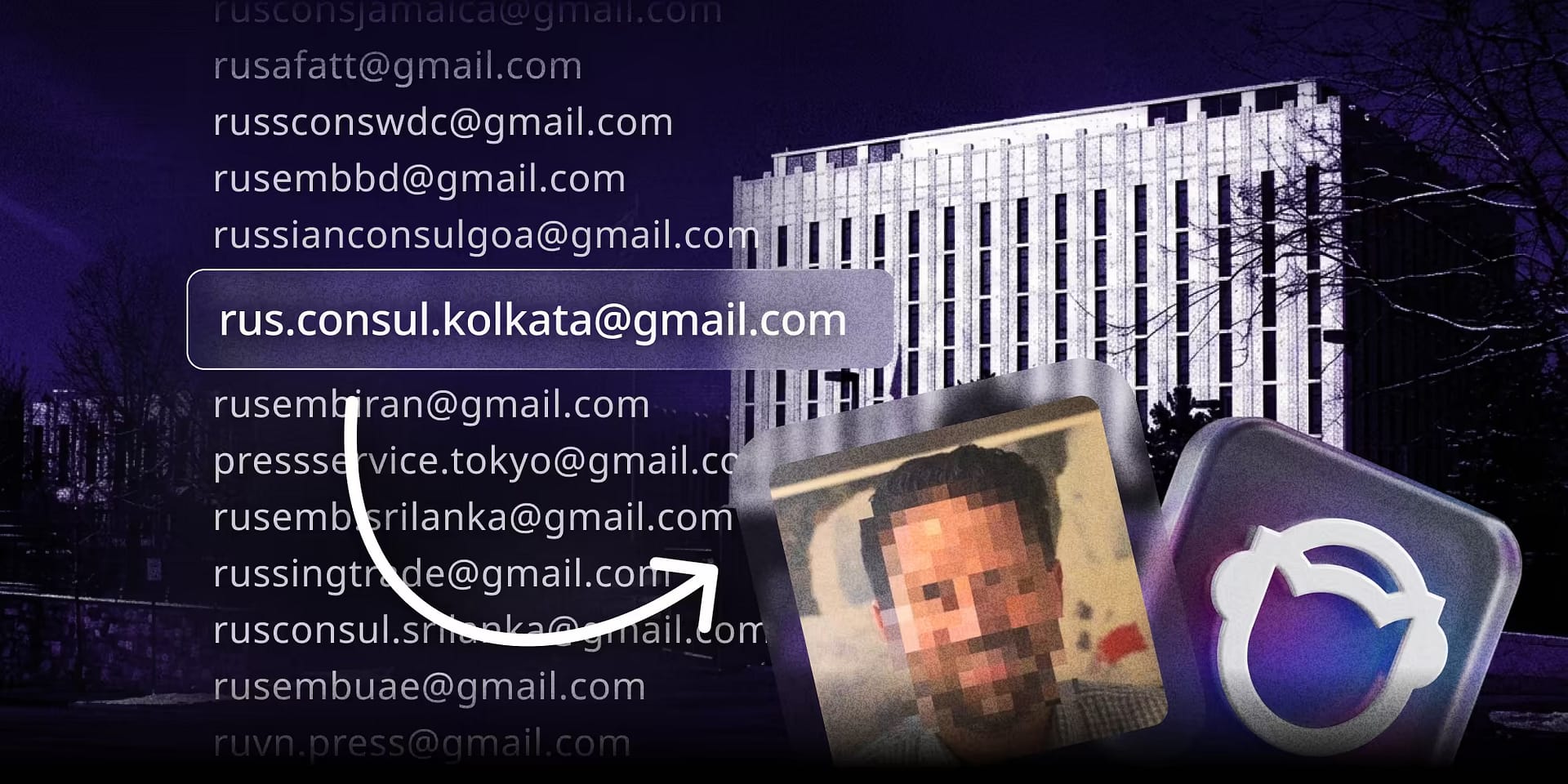
Russia’s Email Problem: How OSINT Exposes Russian Embassies Worldwide | OSINT Case Study
Using OSINT Industries, Jordan analyzed 342 Russian embassy emails. This Russia-focussed email OSINT investigation revealed breaches, poor OpSec, and a high likelihood of exposure.