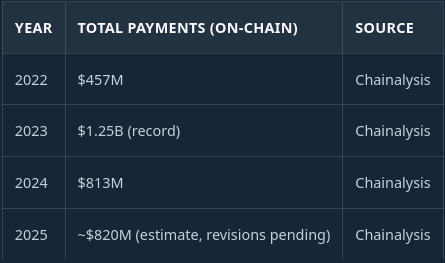
Ransomware revenue was roughly $820 million in on-chain payments last year, according to Chainalysis. Down from the $1.25 billion record in 2023, but still one of the more reliable criminal revenue streams on the planet.
Eighty-five extortion groups competed for that market in Q3 2025, per Checkpoint. Forty-seven of them claimed fewer than ten victims each.
That ratio kept nagging at me and seemed off when just spotting it. More than half the players in an $820 million market are barely registering activity. If this were a legitimate industry, most of those operations would have already folded. So I started pulling the actual cost data — from leaked internal chats, from affiliate programme pages that are still live on the dark web right now, from quarterly reports by Chainalysis and Coveware — and tried to answer a question that gets surprisingly little attention: what do the unit economics of a ransomware operation actually look like?
Not from a law enforcement angle. Not victim impact. Strictly the P&L. Market research before a start-up.
Every figure in this piece is sourced from public reporting, leaked internal documents, or dark web infrastructure I can observe directly. This is financial analysis, not a manual. OSINT in action.
The Market
On a slide deck, the TAM looks attractive.

But the conversion funnel is collapsing. The share of victims who actually pay dropped from 78.9% in 2022 to roughly 20% by Q4 2025 — an all-time low tracked by Coveware. Exfiltration-only attacks, where the operator steals data without encrypting anything, performed even worse at 19%.
Attack volume is rising at the same time. Leak-site claims up 50% year-on-year in 2025. More attacks, fewer payments. The market is growing and becoming less profitable simultaneously.
The median ransom paid sits at $59,556 for 2025 full-year (Chainalysis). The average is $591,988 in Q4 2025 Coveware case data, but that figure is dragged up by a handful of seven-figure outliers — one Fortune 50 company paid $75 million in a single transaction in 2024 (Admin by Request). Strip out the top end and most operators are chasing five-figure payments from companies with about 200 employees. Sixty-nine percent of Coveware’s Q4 2025 caseload was companies under 1,000 staff. Not an enterprise play. A volume business targeting organisations big enough to pay and small enough to lack mature defences.
Here is the number that changes everything else in this article: 90% of ransomware attacks fail or produce zero losses, per AAG-IT’s analysis of detection and outcome data.
Nine out of ten go nowhere.
The Competition
Top ten groups account for 56% of published victims, down from 71% at the start of 2025. Akira and Qilin together held 44% of attacks in Q3 before the market fragmented further into Q4.
At the other end, those 47 groups with fewer than ten victims each — some are new entrants testing the waters, some spun up and failed to gain traction and will quietly disappear. There is not much daylight between the two categories.
The barrier to entry has never been lower. DragonForce’s registration page lets you pay $500 in Monero or Bitcoin and walk away with a customisable ransomware locker, a leak blog, and a negotiation portal inside an hour. That low barrier is exactly why the market is this crowded. It is also why most operators are failing.
Five Revenue Models
The market has converged on a handful of structures. Each one has real operators running it right now, and each has a different answer to the question of where margin comes from.
1. Subscription (Tool Seller)
Sell the kit for a flat fee. The affiliate keeps everything they collect.
A French-language operation called ContFR currently runs three tiers: €400 for 30 days with one ransomware modification, €1,200 for six months with ten modifications, €2,200 for a full year with unlimited modifications and a support chat. Payload embedded in a PDF. Windows and Mac, no Linux.
Historically this bracket includes Stampado at $39 for a lifetime licence back in 2016, Philadelphia at $389, RaaSBerry with tiers from $60/month to $650 for three years. None of those names are around anymore.
The problem is structural. Even at €2,200 a year you need dozens of subscribers to cover a small dev team, and you never participate in a $2 million ransom. Revenue is hard-capped at subscriber count times price. Almost nobody runs this as a primary model anymore — the ceiling is too low. Only profitable as hobby project from your basement.
2. Commission (Profit-Share)
The dominant model. Operator provides the toolkit, the infrastructure, the leak site, sometimes the negotiation support. Affiliate executes the attack. They split the ransom.
LockBit’s current affiliate rules page lays it out: operator takes 20%. For ransoms over $50,000, two wallets generate automatically — 80% affiliate, 20% LockBit. If LockBit handles the negotiation directly, the affiliate’s share drops to somewhere between 50% and 70%. They also run a bug bounty on their own code, which tells you something about how they think about product quality.
The splits across major groups cluster tightly around the same range:
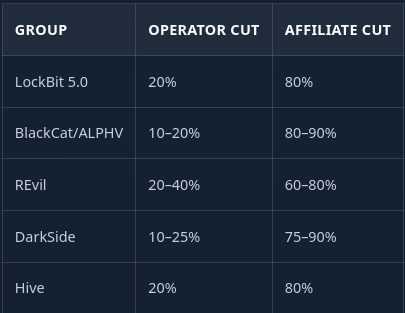
DarkSide ran a sliding scale — 25% on ransoms under $500,000, dropping to 10% on anything above $5 million. REvil started affiliates at 70% and bumped them to 80% after three successful payments. Loyalty programme logic applied to extortion.
Works at volume. Falls apart when your affiliates stop producing. It would be interesting to know what the turnover rate is for affiliates and projects per affiliate per year.
3. White-Label Platform (Franchise)
This is where it gets interesting, and this is the model I think most people covering ransomware are underestimating.
DragonForce calls itself a “Ransomware Cartel” and operates as a platform. For $500 in registration — refundable after your first payout — you get customisable lockers for Windows, ESXi, BSD, and NAS. A leak blog you can brand however you want. File hosting through MEGA, SFTP, Pixeldrain, or Storj. A ticket-based support system. Free NTLM and Kerberos decryption tools. A call service for victim communication.
Their pitch, quoted directly: “You no longer have to work under our brand. Now you can create your own brand under the auspices of DragonForce.”
RansomHub already migrated to their infrastructure under this arrangement.
What makes this different from the commission model is the economics underneath. DragonForce provides the platform and absorbs the infrastructure cost. They take 20% from every ransom across every brand running on their stack. Costs are semi-fixed. Revenue scales with each new “project” that joins. From a business model perspective, this is the most defensible structure in the current market — and they know it.
They have also started running a data analysis service through a partner called “NetFold.” A 9% commission for pre-attack data analysis bundled into the locker, 12% for cases built entirely from exfiltrated data without encryption. Monetising the intelligence layer, not just the extortion.
4. Salaried Operation (Corporate)
No affiliates. Hire everyone. Keep 100%.
Conti ran this until their internal communications leaked in February 2022. What came out looked like the org chart of a mid-sized tech company: 62 to 87 salaried employees across development, QA, HR, finance, OSINT, and reverse engineering. Average salary ran $1,800 to $2,500 a month. Middle managers made roughly $80,000 a year. Negotiators took 0.5% to 1% commission on each payment. Staff were paid in Bitcoin on the 1st and 15th. Employee-of-the-month awards. Performance reviews. A $100 fine if you missed a payment deadline.
Monthly payroll for 62 people: $164,800. Annual operating cost per Rapid7: approximately $6 million.
Full control, no affiliate drama. But payroll hits regardless of whether ransoms come in, and the Conti leaks showed genuine cash flow stress even at their scale. Ryuk, their predecessor operation, earned $61 million in its first year per the FBI — a healthy 10:1 revenue-to-cost ratio. Sustaining that required roughly 100 staff and uninterrupted attack volume. The moment either slipped, the pressure was immediate. Thats a lot of stress for an average payday.
5. Exfiltration-Only (No Encryption)
World Leaks runs this model. Their blog states the project “arose from a fundamental disagreement over encryption.” They steal data and threaten publication. No ransomware deployed, no decryption keys, no encryptor to build or maintain.
Their site pulls 9,102 visitors in the last 24 hours, 56,847 weekly, 235,795 monthly. They recently added HTTP Range Header support so interrupted downloads can resume. They are running leak infrastructure the way a product team would run a download portal — which is a strange sentence to write, but here we are.
Lower technical barrier is the draw. No encryptor to develop and maintain, no decryption support tickets. But the payment rate for exfiltration-only attacks hit 19% in Q3 2025, Coveware’s lowest on record for that category. Without encrypted systems creating operational urgency, victims are more willing to absorb the reputational damage and walk away.
Cost Structure
What does it cost to stand up and run one of these operations? The numbers are smaller than you might expect.
Small team (2–5 people): Two or three developers at $2,000 to $2,500/month based on the Conti salary range. Bulletproof hosting for a C2 server and leak site runs $300 to $600. VPN and domains on top. Monthly burn lands around $5,000 to $9,000 before purchasing any initial access to targets.
Mid-tier (15–30 people): Dedicated dev, negotiation, support, and OSINT staff. Multiple bulletproof hosting providers for redundancy. Phishing infrastructure at $400 per million emails if you are running your own campaigns. Initial access broker purchases at $500 to $3,000 per target — though the average price has cratered to $439 in Q1 2026 (Darkweb IQ / Chainalysis), down from $1,427 in Q1 2023. Monthly burn: $30,000 to $85,000.
Enterprise (60–100 people, the Conti model): All of the above plus HR, finance, management overhead, volume IAB purchasing, and the kind of operational testing budget that a well-funded startup would recognise. Monthly burn: $140,000 to $200,000. Annualised: $1.7M to $2.4M. Conti’s actual figure was closer to $6 million, which included aggressive hiring and redundant infrastructure.
The Laundering Tax
This is the line item most ransomware analyses leave out entirely, and it is the one that breaks the economics for the majority of operators.
Receiving $500,000 in cryptocurrency is not the same as having $500,000 you can spend. You need to convert it without being traced, arrested, or having your wallets seized mid-transfer.
Crypto mixers charge 1–3% per transaction, but the infrastructure is eroding. ChipMixer was seized. Tornado Cash sanctioned. Sinbad indicted. Samourai Wallet operators charged for processing over $100 million in ransomware proceeds. Cross-chain bridges are filling some of that gap, but under growing scrutiny from the same agencies that took the mixers down.
The real cost is converting crypto to fiat. Money mules — people who receive the crypto, convert to cash, and pass it along through layers of accounts — take 50% to 60% of the total. You lose half your revenue to get money you can actually use. Thirty-nine percent of ransomware flows still route through centralised exchanges (Chainalysis), but KYC requirements and law enforcement cooperation at the exchange level mean seizure risk hangs over every transaction.
Here is what that does to a median ransom payment:

A median ransom puts $5,777 of usable cash in the operator’s pocket. That is the real number sitting behind the $820 million headline figure.
Break-Even
This is where it falls apart for most groups.
Combine the 90% technical failure rate with the 20% payment rate and you get a net success rate of roughly 2%. Two payments per hundred attempts. I went back and forth on whether to trust the 90% figure — it is from AAG-IT and based on older detection data — but even if you are generous and call it 80% failure, the net rate only climbs to 4%. The math is still brutal.
After laundering, planning around median payments ($59,556):

A mid-tier commission-based operation relying on median-range payments needs around 435 attack attempts per month after laundering costs. That is 14 a day, every day, with no breaks and no dry spells.
If you land average-sized payments ($591,988) instead, a mid-tier operator needs fewer than one successful hit per month. But planning around the average is how startups die. Averages are pulled by rare outliers. The median tells you what most months actually look like, and most months look like five-figure payments if you are lucky enough to get paid at all.
LockBit’s leaked admin panel, exposed in May 2025, gives us the closest thing to a verified P&L in the industry. Between December 2024 and April 2025, confirmed earnings were roughly $2.37 million over five months. LockBit’s 20% cut: about $456,000, or $91,000 a month. That barely covers a mid-tier cost base. And this is LockBit — the most recognised name in the market. If their numbers look like that post-disruption, the 84 groups below them are doing worse.
SWOT
Strengths
- Entry cost as low as $500 (DragonForce) or €400 (ContFR)
- Cryptocurrency enables pseudonymous cross-border payment
- IAB prices collapsing — $439 average per target, Q1 2026
- Platform models make infrastructure semi-fixed while revenue scales with each new affiliate brand
Weaknesses
- 90% technical failure rate before any payment question arises
- 20% payment rate among victims who are actually hit (Q4 2025)
- Combined net conversion: ~2% of attempts produce revenue
- Laundering eats 50–60% of whatever does come in
- Cash flow is volatile in a way that makes SaaS founders look spoiled — one big hit, then silence for weeks
- 41% of paying victims do not recover all their data (Barracuda), meaning the product often fails to deliver what it implicitly promises
- Your workforce operates outside all employment law, and the best ones will leave for whoever offers 90/10 next quarter
Opportunities
- AI-assisted tooling (80% of 2025 attacks used AI components, per MIT)
- White-label models keep lowering the barrier for new entrants to join existing platforms rather than build from scratch
- Regulatory pressure from GDPR Art. 33–34 notification requirements creates a payment incentive that exists independently of encryption
Threats
- Hive dismantled (Jan 2023), LockBit disrupted (Feb 2024), ALPHV infrastructure seized — the cadence is accelerating
- 97% of encrypted organisations recovered data without paying in 2025 (Sophos)
- The entire crypto laundering stack is under systematic enforcement pressure, with each seized mixer or sanctioned bridge narrowing the off-ramp options
- BlackCat exit-scammed their own affiliate over $22 million from the Change Healthcare attack — the trust model between operators and affiliates is structurally broken, and there is no arbitration mechanism
- One insider leak or one admin panel breach ends the operation. Conti and LockBit both learned this. The next group will too.
Why Your Ransomware Startup Will Probably Fail
Forty-seven of 85 groups claimed fewer than ten victims last year.
At median payments after laundering, the per-hit return to a commission-based operator is under $6,000. You need hundreds of attack attempts monthly to make the numbers work. You need affiliates who are skilled, reliable, and consistently active — recruited from a labour pool where your best talent can switch to a competitor the moment someone offers a better split, and your worst will draw law enforcement attention that lands on you.
Infrastructure gets seized. Affiliates defect. Someone on the inside gets upset about a missed Bitcoin payment and dumps your entire chat history. Your biggest ransom gets frozen on a centralised exchange. The $22 million payday gets stolen by your own platform operator before you see a cent of it.
The operations that actually make money share a short list of characteristics: scale, brand recognition, and enough operational discipline to sustain hundreds of attacks per month while managing a workforce that exists entirely outside any legal framework. There are maybe five to ten groups that fit that description. Everyone else is running a criminal startup with a 2% conversion rate, a 50% transaction fee, and a customer base that gets better at refusing to pay every single quarter.
The $820 million headline is real. What reaches any individual operator’s pocket — in usable currency, after costs, after laundering, after failure rates, after the affiliate takes 80%, after law enforcement seizes the mixer you used last month — looks nothing like that number.
The access brokers, credential markets, and leak sites described in this article are not theoretical. They are live infrastructure, trading data on real companies every day. If you want to know what that ecosystem already holds on your organisation, a Corporate Audit maps the full surface.
Originally published at https://privacyinsightsolutions.com on March 24, 2026.
RaaS Business Plan: Ransomware Unit Economics 2026 was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.