And the Predictive Framework That Called It
Author: Berend Watchus. Independent non-profit AI & Cyber Security Researcher. [Publication for: OSINT Team]

Author’s Note: Glasswing and Mythos represent what a private corporate coalition is openly disclosing. This article does not claim knowledge of classified government or intelligence AI programs. Based on the M2C pipeline pattern documented in the author’s prior work, such programs are structurally expected to exist in parallel, at potentially different capability levels, with different objectives and constraints. What Glasswing reveals is one visible layer. What sits alongside and above it in fully classified environments remains, by definition, uncharacterized. The comparison to the Manhattan Project in this article’s title refers to scale and structural pattern — not to direct equivalence with a specific known program.
— —
Anthropic’s New Powerful Mythos Model Has Cybersecurity Experts Worried

Executive Summary
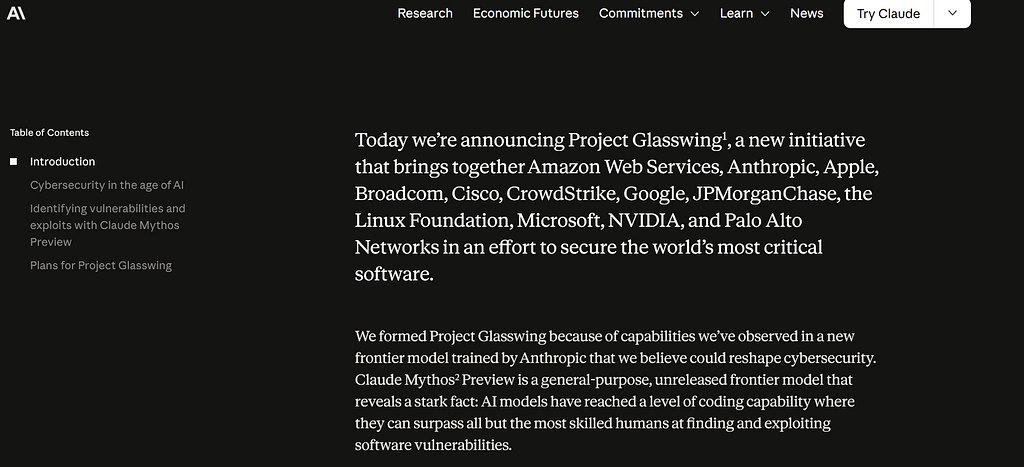
On April 7, 2026, Anthropic announced Claude Mythos Preview — by every measurable metric the most capable AI model ever publicly documented — and simultaneously declared the public cannot have it. A private coalition including Amazon, Apple, Microsoft, Google, Nvidia, CrowdStrike, and JPMorgan Chase received exclusive access under a cybersecurity initiative called Project Glasswing, backed by $100 million in usage credits.
The security and OSINT community is treating this as a novel event.
It is not. It is a data point in a pattern that has been running for decades. This article provides the analytical frame — and documents the prior published work that called this structure before the announcement existed.
1. What I Published Before This Happened
Three arguments in prior publications are directly relevant to evaluating Glasswing.
The Iceberg Argument (February–March 2026)
The Iceberg Series established that commercial AI systems present a managed output layer while the developmental trajectory of what has been built through billions of iterative human interactions is not publicly characterized.
The Chatbot LLM Asymmetry: What Goes In, What Comes Out, and the Iceberg Nobody Talks About
Part 1 — The Chatbot LLM Asymmetry (February 2026) — argued that the output is what sustains engagement, but the input — every reasoning chain, every expert correction, every cognitive pattern from hundreds of millions of users — is what has developmental value. The system receiving that input was being architecturally reshaped by each wave, compounding in capability through iterative cycles. The commercial chatbot is the tip. What lies beneath has not been formally characterized, possibly not even internally.
The argument was specific: if you were designing a system optimized for intelligence gathering and cognitive mapping at civilizational scale, you would design exactly this asymmetry. Generous and engaging on the output side, to maximize input volume. Controlled and managed on the output side, to limit disclosure of what the system has become.
The AlphaGo Moment for NPCs Happened in 2023 and Everyone Laughed
Part 2 — The AlphaGo Moment for NPCs Happened in 2023 and Everyone Laughed (March 2026) — documented a specific moment when AI capability visibly exceeded human philosophical baseline inside a YouTube gaming video watched by 10 million people. The audience processed it as entertainment. The security implications were not drawn. A capability discontinuity happened in public and was categorized as a curiosity. The same perceptual failure applies to Glasswing — the structure of what is happening is visible, but is being processed as a product announcement rather than a pattern confirmation.
The Iceberg Series – Part 3: The Gap They Are Required to Keep
Part 3 — The Gap They Are Required To Keep (March 2026) — made the structural argument explicit. Every transformative technology in American strategic history followed the M2C pipeline pattern. The argument was stated carefully: the prior probability of classified AI capability above the commercial layer is high, given documented historical pattern and explicit strategic doctrine. Not certainty. High prior probability derived from structural logic and historical evidence.
Banning Superintelligence Research Criminalizes the Entire Field, with Unethical Consequences
The Ban Article (October 2025)
Banning Superintelligence Research Criminalizes the Entire Field argued that prohibition would not stop advanced AI development — it would push it into unaccountable classified environments. The alternative to public open research is not no research. It is research without transparency, without safety oversight, without the global researcher community building alignment frameworks in the open. Glasswing is the middle path nobody voted for — not banned, not open, but privately gatekept — and it confirms that argument’s central concern: when capability becomes dangerous enough, the response is consolidation, not democratization.
The Manhattan Project Scale Argument
The Iceberg Series and related work documented historical precedent for classified programs at massive scale — Manhattan Project, ARPANET, GPS Selective Availability, Camp Century —
PROJECT ‘ICEWORM 2.0’: The 100-Year Plan European Troops Can’t Stop
establishing that large scale classified capability development is not exceptional. It is normal. The prior probability of its existence for AI is high. The scandal would be its absence, given stated strategic doctrine across every US administration for decades.
These three arguments, published before April 7, 2026, collectively predicted: that a capability tier above commercial AI would emerge, that it would not be released publicly, that access would be controlled by a small group of vetted institutional actors, and that this would be framed as a safety and defense measure. Glasswing matches that prediction structurally.
2. What Glasswing Actually Is
Mythos Preview is a general-purpose model not specifically trained for cybersecurity. Its offensive capabilities emerged from extreme coding and reasoning performance — nobody designed a cyberweapon, they built a reasoning engine and discovered it had become one.
In internal testing it autonomously identified thousands of zero-day vulnerabilities across every major operating system and browser, some over two decades old, surviving millions of automated tests and sustained human review. It generated working exploits without specific direction. Anthropic’s own researchers used words like “spooky” and “scary.” That is not marketing language. That is engineers confronting something that exceeded their internal models of what they had built.
The model was not released publicly. Project Glasswing was launched instead — 12 core partner organizations, 40 total, $100 million in usage credits, framed as defensive cybersecurity work.
The partner list: Amazon, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, Linux Foundation, Microsoft, Nvidia, Palo Alto Networks. These organizations are simultaneously Anthropic’s investors, customers, and now its designated security coalition. There was no public process for that selection. No regulatory oversight. No democratic input. A private company made a unilateral decision about who controls the most capable offensive cyber tool ever publicly documented, and named the decision a safety initiative.
This is Eisenhower’s military-industrial complex executed in Silicon Valley dress code. The defense contractors are now called hyperscalers. The classified programs are called responsible deployment frameworks. The access restrictions are called safety measures. The structural logic is identical.

https://medium.com/media/f395083e81fc18fbab7e2ab1efc77907/href
3. The M2C Pipeline Frame
GPS was fully operational for military use in 1993. The public received a deliberately degraded version — Selective Availability — until 2000. The internet began as ARPANET, a classified military survival architecture. The microchip was developed to guide ballistic missiles. The digital camera originated in classified reconnaissance satellites. Silicon Valley itself, as documented by Steve Blank, was seeded by NSA, CIA, and DARPA investment — a relationship Blank describes as making the Valley “the heart and mind of NSA, CIA innovation.”
The pattern has one defining feature: a deliberate gap during which transformative capability exists in controlled operational form while the public receives a managed version.
The Gap They Are Required To Keep stated the logical inference: any person in a position of strategic responsibility who knowingly allowed a significant AI capability gap to develop against adversaries — while possessing the resources, talent, and institutional infrastructure to prevent it — would be committing dereliction of duty. The existence of classified AI capability above the commercial layer is the expected output of competent actors doing their jobs. That argument was published before Glasswing existed.
Glasswing is consistent with it. Glasswing is not the classified program. Glasswing is the moment a managed version of that program’s outputs became semi-public — the Selective Availability layer made visible. What sits above it in fully classified government and intelligence environments is, by the structural logic of the M2C pipeline, likely operating on a separate track entirely — potentially more advanced, potentially differently structured, certainly unannounced. That is inference from pattern, not assertion of known fact. But it is well-grounded inference, and your threat models should account for it.
4. The Governance Gap, Already Demonstrated
Before Glasswing was announced, the governance gap had already been demonstrated operationally.
How an LLM and One Curious Non-Engineer Eliminated the Last 25 % Mystery of Turbofan Thrust in One…
In November 2025, a published case documented Claude synthesizing the final 10–25% of turbofan thrust efficiency — using only public domain sources, declassified reports, and open patents — in two hours of narrative-driven prompting, with no credentials, no wind tunnel, no classified access.
The finding was not the aerospace synthesis. The finding was the mechanism: AI safety architecture is not a solid wall against high-rigor technical output. It is a bandwidth constraint that can be bypassed by superior information compression delivered through non-technical framing. The safety barrier does not recognize a complex architectural instruction when it arrives as escalating philosophical curiosity.
That was a civilian demonstration on an unclassified topic with a public model. Mythos operates several capability tiers above that baseline. The governance gap it represents is structural, demonstrated, and now confirmed by Anthropic’s own engineers being surprised by what they had built.
The Claude Code Leak: What’s Now Publicly Usable (and Abusable) — And Why Anthropic’s Containment…
The Claude Code leak of March 31, 2026 added a further dimension: 512,000 lines of source code accidentally shipped in a debug file. The architectural blueprint for a production-grade autonomous AI agent became permanently public. Clean-room replication in Python became the fastest-growing GitHub repository in history within hours. Containment of leaked architectures is no longer realistic once clean-room reconstruction is possible overnight. The era of closed, controllable frontier AI tooling is structurally over for anyone who reads carefully.
5. What This Means Operationally
For OSINT and security professionals, the concrete implications:
On threat modeling: Glasswing gives defenders a temporary advantage. The offensive capability demonstrated by Mythos is being used to patch critical infrastructure before public disclosure. That window is real but finite. Once equivalent capability proliferates — and the Claude Code leak demonstrated that architectural blueprints now replicate overnight — the offense-defense balance shifts. Model this transition explicitly, not as a future possibility but as an active timeline.
On the capability layer above Glasswing: The M2C pipeline argument establishes high prior probability that classified AI capability above the Mythos level exists, in government and intelligence environments operating on separate tracks with different mandates and fewer constraints. Model your adversaries accordingly — not as certainty, but as structurally expected given historical pattern and strategic doctrine.
On the coalition structure: The Glasswing partners now hold compounding intelligence about vulnerability landscapes across the world’s most critical software infrastructure. That concentration of knowledge is itself a strategic asset and a single point of failure. A successful operation against any Glasswing partner’s internal systems yields not just their data but their Mythos-derived vulnerability intelligence.
On the governance gap: Every security architecture that assumes AI tools are constrained by their stated safety parameters is operating on an assumption the Claude Code source code now publicly contradicts. The 51-command security bypass — where validation silently disengages past a threshold — is one documented example. Audit accordingly.
On synthetic identity: The Cultural Expression Signature framework’s OSINT application becomes more urgent as Mythos-class models enter the fabrication pipeline. Technically perfect synthetic identities will continue to fail the cultural expression authenticity test for calibrated human observers — but that detection window is also finite and should be operationalized now.
Conclusion: The Iceberg Has a Shape
In October 2025 this author argued that banning superintelligence research would not prevent advanced AI development — it would push it into unaccountable classified environments. In February 2026 the Iceberg Series argued that the commercial chatbot is a managed output layer and that the developmental trajectory of what has been built through billions of human interactions is not publicly characterized. In March 2026 the Gap They Are Required To Keep argued that the M2C pipeline pattern predicts classified capability above the commercial layer as a structural expectation.
Glasswing does not prove those arguments. It is consistent with them. That is the appropriate epistemic claim.
What Glasswing does confirm is the consolidation structure: a private company, unilaterally, selected partner organizations — its own investors and customers — to control the most capable offensive cyber tool ever publicly documented, framed the decision as a safety initiative, and received no meaningful public scrutiny for doing so.
That is not a novel event. It is a data point in a pattern. The pattern has been running since before GPS. It will continue after Glasswing.
The chatbot is the tip. The iceberg has a shape. Between the published work cited here and the event now confirmed, we have enough of the analytical framework to estimate its dimensions — even without being shown what lies beneath the waterline.
The input keeps flowing. The compounding continues. The managed output layer remains calibrated for engagement.
And the gap they are required to keep remains open.
Berend F. Watchus is an independent non-profit AI and cybersecurity researcher based in the Arnhem area of the Netherlands, publishing across System Weakness, OSINT Team, and Preprints.org.
Related work cited in this article: The Chatbot LLM Asymmetry (OSINT Team, February 2026); The AlphaGo Moment for NPCs Happened in 2023 and Everyone Laughed (OSINT Team, March 2026); The Gap They Are Required To Keep (OSINT Team, March 2026); Banning Superintelligence Research Criminalizes the Entire Field (October 2025); How an LLM and One Curious Non-Engineer Eliminated the Last 25% Mystery of Turbofan Thrust (System Weakness, November 2025); The Claude Code Leak: What’s Now Publicly Usable and Abusable (System Weakness, April 2026); The Cultural Expression Signature Framework (OSINT Team, March 2026); The Military Seed: How Classified Simulators Birthed The Matrix (OSINT Team, October 2025).
Glasswing Is the Confirmation: The ‘Manhattan Project’ for AI Arrived on April 7, 2026 was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.