Proxy Resilience and Reflexive Control

As of late March 2026, Russia’s war in Ukraine has entered its fifth year as a brutal war of attrition. Moscow continues to make incremental territorial gains at enormous human and material cost, yet it is clear that the Russian military is far from the force that launched the full-scale invasion in 2022. Independent estimates place total Russian casualties above one million, heavy equipment losses have depleted decades-old Soviet stockpiles, sanctions have frozen hundreds of billions in assets, and the Kremlin has resorted to recruiting foreign fighters from Africa and elsewhere to sustain its manpower. Conventional wisdom suggests that a weakened Russia lacks the capacity for major new offensives, let alone a direct challenge to NATO.
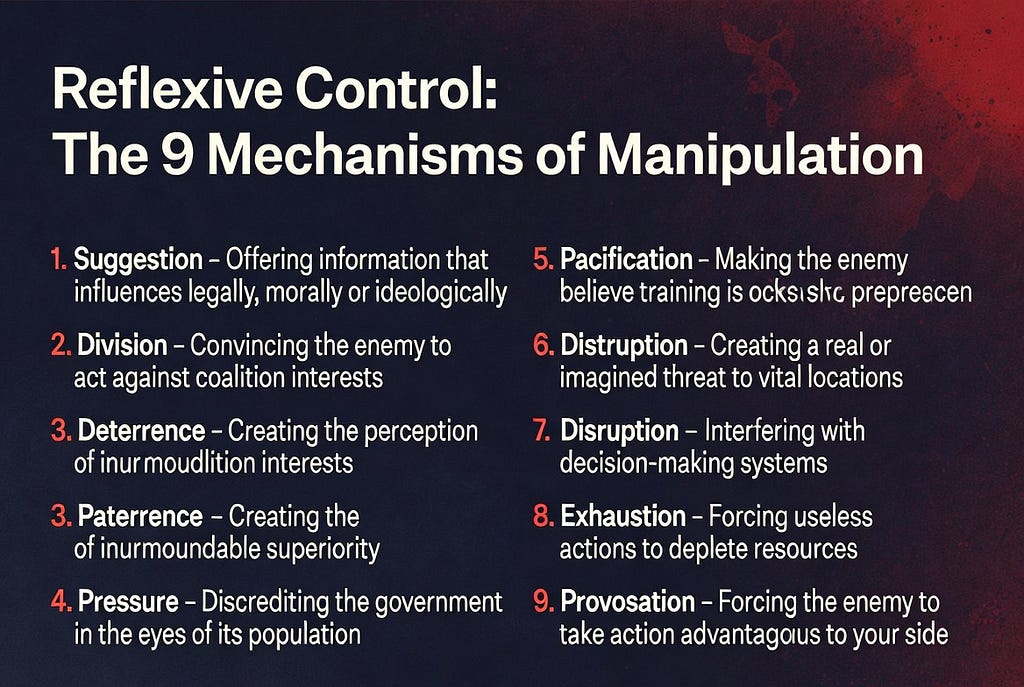
Yet this very weakness has not produced de-escalation. Instead, it has driven a strategic pivot: Russia is doubling down on a prolonged, low-intensity shadow war — a hybrid campaign of sabotage, cyberattacks, disinformation, and proxy operations that stays deliberately below the threshold of open armed conflict. In this environment, traditional military metrics matter less than the ability to impose cumulative costs on the West without triggering Article 5. The goal is not decisive battlefield victory but sustained pressure, societal erosion, and reflexive control — the Soviet-era doctrine of shaping an adversary’s decisions by feeding it manipulated information until it acts against its own interests.
At the heart of this shadow-war toolkit lies a class of dual-use cyber infrastructure: commercial providers that operate under Russian jurisdiction while offering globally distributed scrubbing, hosting, and denial-of-service protection. Marketed as legitimate cybersecurity services, these entities provide resilience to a broad client base — including state-aligned proxies that Western platforms routinely de-platform. The arrangement is elegant in its asymmetry. Russia supplies the protective layer at minimal direct cost, proxies supply the operational labor and plausible deniability; and the West absorbs the long-term economic, psychological, and societal damage.


A public case in point is the repeated migration of Iranian state-linked hacktivist actors — most notably groups assessed by the U.S. Justice Department and multiple Western threat-intelligence firms as affiliated with Iran’s Ministry of Intelligence and Security (MOIS). After domain seizures and law-enforcement actions in mid-March 2026, these actors swiftly re-established their leak, doxxing, and extortion operations behind Russian-protected infrastructure. The pattern is not isolated; it exemplifies how Moscow’s commercial cyber ecosystem enables aligned proxies to maintain operational continuity against Western targets while preserving deniability for the Kremlin.
This article examines how such dual-use infrastructure has become a central pillar of Russia’s strategy in an era of conventional weakness. It argues that the real danger lies not in spectacular kinetic escalation but in a destructive, long-term confrontation landscape — one shaped by proxy resilience, reflexive control, and information operations that slowly corrode societal cohesion. The following sections explore Russia’s current strategic reality, the logic of hybrid prolongation, the mechanics of dual-use enablement, the underestimated societal threat, and the realistic counters available to the West.
Russia’s Strategic Weakness in 2026
Four years into its full-scale invasion of Ukraine, Russia finds itself locked in a war of attrition that has profoundly degraded its conventional military power. What began as a lightning campaign intended to topple Kyiv in weeks has become a grinding meat-grinder that consumes men, machines, and money at a pace Moscow cannot sustain indefinitely. Open-source intelligence and Western assessments paint a consistent picture: Russia is not on the verge of collapse, but it is strategically exhausted in ways that make any major new conventional adventure , let alone a direct challenge to NATO highly improbable in the near to medium term.

The human cost is staggering. Ukrainian General Staff figures, corroborated by independent Western estimates, place total Russian personnel losses (killed, wounded, missing, and captured) above 1.29 million as of late March 2026. Even conservative analyses from the U.S. and European intelligence communities put the figure in the 1.0–1.4 million range, with between 230,000 and 430,000 killed. This represents the near-total depletion of Russia’s pre-war professional contract soldiers and a large slice of its prime-age male population. To compensate, the Kremlin has turned to increasingly desperate measures: lowering the conscription age, offering large cash bonuses, and aggressively recruiting foreign fighters. Verified reports document at least 1,400–1,800 recruits from more than 35 African countries (despite of the 11.000–14.000 North Korean soldiers, 6.000 already died) alone between 2023 and early 2026, many lured by false promises of non-combat jobs only to be thrown into high-risk assault roles. Similar recruitment drives have targeted Nepal, Cuba, India, and parts of the Middle East. These foreign contingents provide short-term numbers but lack training, cohesion, and loyalty — further eroding the overall quality of Russian forces.

On the equipment side, the losses are equally catastrophic. Ukraine claims to have destroyed or captured more than 11,800 Russian tanks since February 2022 — a figure that exceeds the entire current active tank inventory of the United States and most of NATO combined. Russia has responded by cannibalizing decades-old Soviet-era stockpiles, reactivating T-62 and T-55 tanks from long-term storage, and producing new or modernized vehicles at a rate of roughly 30–35 per month. While this output is impressive on paper, it is far below what would be required to replace losses while simultaneously maintaining reserves for any future large-scale operation. The same pattern repeats across artillery, armored vehicles, aircraft, and naval assets: Russia is burning through its Cold War inheritance faster than it can replenish it.
Economic pressure compounds the military strain. Since 2022, Western sanctions have frozen roughly $285–300 billion in Russian central-bank assets and denied Moscow an estimated $450 billion in energy revenues. While the Russian economy has shown surprising short-term resilience — fueled by wartime military spending and parallel imports through China, Turkey, and India — the long-term picture is bleak. The war economy distorts civilian sectors, drives inflation, and creates structural weaknesses that will take years to repair. Oil and gas revenues, still the backbone of the budget, remain vulnerable to price fluctuations and enforcement of price caps. The Kremlin’s own internal projections acknowledge that sustaining current spending levels beyond 2026–2027 will require painful trade-offs.
Domestic sentiment reflects this exhaustion. Independent polling (where it still occurs) shows a majority of Russians continuing to express nominal support for the “special military operation,” yet the mood is one of passive acceptance rather than enthusiasm. War fatigue is widespread, especially among younger cohorts that have borne the heaviest losses. Public protests remain rare and heavily suppressed, but the steady trickle of returning wounded soldiers, funeral notices, and stories from African recruits has begun to seep into everyday discourse. The regime has managed to insulate itself from mass discontent through propaganda and repression, but the underlying demographic and social damage is real.
Taken together, these factors explain why most serious military assessments including those from German, Baltic, and NATO planners — treat a Russian conventional attack on NATO territory by 2029 as a worst-case planning scenario rather than a likely event. Russia’s forces are pinned down in Ukraine, its industrial base is overstretched, its economy is under sanctions stress, and its population is war-weary. Moscow retains the ability to conduct limited hybrid operations and to reconstitute slowly, but it lacks the surplus capacity for a new, high-intensity conventional campaign against a prepared alliance.
This conventional weakness is precisely what has driven Russia’s strategic pivot toward the shadow war we see today. Unable to win on the battlefield, Moscow has chosen to impose costs through deniable, low-intensity tools — sabotage, cyberattacks, disinformation, and proxy operations. The next sections examine the logic of this prolonged confrontation and the critical role dual-use cyber infrastructure plays in sustaining it.
The Logic of Prolonged Confrontation
Russia’s conventional weakness does not signal retreat; it has instead produced a deliberate strategic recalibration. Unable to achieve decisive victory on the Ukrainian battlefield or project power against a prepared NATO, Moscow has chosen to prolong the conflict through hybrid means — a shadow war that exploits the seams between peace and open hostilities. This is not improvisation. It is a return to a well-established Russian strategic tradition: when direct military superiority is unavailable, impose costs asymmetrically, erode the adversary’s will, and shape the information environment to compel favorable outcomes.

At the doctrinal heart of this approach lies reflexive control, a concept rooted in Soviet military science and refined in post-Soviet Russian thinking. Developed in the 1960s by Soviet theorists such as Vladimir Lefebvre and later operationalized by the GRU and FSB, reflexive control is the art of feeding an adversary carefully curated information so that the target reaches a predetermined decision — one that appears rational to it but serves the controller’s interests. Unlike crude propaganda, reflexive control is interactive and predictive. It does not merely broadcast a message; it creates feedback loops that influence policy debates, public opinion, and even internal decision-making processes. In modern practice, this manifests through timed leaks, disinformation campaigns, amplified social-media narratives, and proxy actions designed to make Western governments question their own support for Ukraine or fracture alliance cohesion.
The logic of prolonged confrontation flows directly from Russia’s material constraints. A direct conventional attack on NATO territory would be suicidal: the alliance’s combined defense spending, technological edge, and industrial base far outmatch Russia’s depleted forces. Instead, hybrid tools offer Moscow three decisive advantages:
- Deniability and low cost: Sabotage operations, cyberattacks, and proxy campaigns can be outsourced to criminal networks, state-aligned hacktivists, or commercial infrastructure providers. Attribution is difficult and slow, allowing Russia to impose real damage while maintaining the fiction of non-involvement. The financial and human cost to the Kremlin is a fraction of what a conventional campaign would require.
2. Sustainability: A conventional war demands massive daily expenditure of men and matériel. A shadow war can be maintained indefinitely. Russia can rotate tactics, test Western red lines, and adjust pressure in response to battlefield developments in Ukraine without risking existential escalation.
3. Cumulative erosion: The goal is not a single decisive blow but the slow degradation of Western societal and institutional resilience. Each successful hybrid incident — whether a railway sabotage, a hospital ransomware attack, or a high-profile data leak — chips away at public confidence, raises defense and insurance costs, and forces democratic governments to divert resources from other priorities. Over years, this creates strategic fatigue.

A recent example of reflexive control in action was the amplification of a March 2025 Telegraph report that President Trump was considering withdrawing U.S. troops from Germany. The story itself was legitimate reporting on policy deliberations. Yet within weeks it was reframed and recirculated by proxy channels as proof that “America is abandoning Europe.” Social-media posts presented it as imminent fact, creating anxiety among European allies and domestic political pressure in Germany and the Baltics. Actors who amplified the narrative often believed they were supporting Ukraine by forcing Europe to “finally pay its fair share.” In reality, the operation exploited existing transatlantic tensions to erode alliance cohesion — a classic reflexive-control outcome achieved through protected information platforms and proxy amplification.
Proxy warfare is the natural extension of this logic. By enabling aligned actors — such as Iranian state-linked groups conducting leak-and-extortion operations — Russia gains reach without direct fingerprints. These proxies serve as force multipliers: they advance shared anti-Western objectives (disrupting supply chains, sowing fear, and shaping narratives) while preserving Moscow’s plausible deniability. The arrangement is mutually beneficial. The proxy gains operational sanctuary and resilience; Russia gains a deniable lever to influence events far beyond the Ukrainian theater.
Cyber operations sit at the center of this ecosystem because they combine speed, scalability, and ambiguity. Russia has invested heavily in “New Generation Warfare” concepts that integrate kinetic sabotage, information operations, and cyber effects into a single continuum. The hybrid campaign in Europe — documented surges in suspected sabotage, drone incursions, and influence activities since 2022 — demonstrates the model in action. It is calibrated to stay below Article 5 thresholds while steadily raising the price of Western support for Ukraine.
This is not a temporary tactic. Russian strategic documents and public statements from senior officials consistently frame the confrontation with the West as existential and long-term. The Kremlin has reframed the Ukraine war as the opening phase of a broader civilizational struggle against NATO expansion and Western dominance. In this worldview, military setbacks on the battlefield are tolerable as long as the hybrid pressure campaign continues to erode the adversary’s political will.
The result is a new normal: a confrontation that is neither peace nor open war. It is a sustained campaign of attrition waged in the gray zone, where Russia’s conventional weakness is transformed into a strategic asset. Unable to win quickly on the ground, Moscow seeks to win slowly through persistence, manipulation, and proxy enablement. This approach maximizes Russia’s remaining strengths — its tolerance for pain, its willingness to operate outside Western norms, and its control over domestic information space — while exploiting the West’s inherent caution and preference for rules-based responses.
The next section examines how dual-use cyber infrastructure has become the critical enabler of this strategy, providing the resilience that allows proxies to operate effectively and reflexive control to function at scale.
Dual-Use Infrastructure as a Strategic Enabler
In the gray-zone environment Russia has embraced since its conventional forces became bogged down in Ukraine, dual-use cyber infrastructure has emerged as one of the most efficient and deniable force multipliers available. These are commercial entities, often marketed as legitimate cybersecurity or hosting providers that operate under Russian jurisdiction while offering services that are attractive to a wide spectrum of clients, including state-aligned proxies and criminal actors. Because they fall under Russian legal and regulatory frameworks (including mandatory cooperation with state security services), they create a structural asymmetry: Western law-enforcement and intelligence agencies face significant hurdles when attempting disruption, while the Russian state retains quiet influence and plausible deniability.

The pattern is straightforward and well-documented in open-source threat intelligence. A provider registers and operates primarily from Russian territory, maintains a globally distributed network of scrubbing centers and anycast routing, and advertises high-capacity DDoS mitigation and “bulletproof” hosting. Customers who are routinely de-platformed by Western cloud and content-delivery networks (CDNs) migrate to these services precisely because takedowns require cross-border legal processes that are slow, politically sensitive, and often ineffective against Russian-based infrastructure. The result is a resilient ecosystem that shields operations without the need for direct state ownership or overt command-and-control.
A clear public illustration of this mechanism is the repeated migration pattern of Iranian state-linked hacktivist personas. Groups assessed by the U.S. Justice Department, Palo Alto Networks Unit 42, Check Point Research, and others as affiliated with Iran’s Ministry of Intelligence and Security (MOIS) have repeatedly used Russian-protected infrastructure to maintain continuity of their leak, doxxing, and extortion campaigns. After Western authorities seized domains in mid-March 2026 (following destructive malware operations and doxxing of individuals linked to Israeli and U.S. targets), the same actors rapidly re-established presence on new domains hosted behind Russian providers. This resilience allows the proxy group to continue psychological operations — publishing stolen data, issuing threats, and claiming high-profile compromises — without losing operational tempo.
Such arrangements serve multiple strategic purposes for Russia. First, they extend reach to partners such as Iran at minimal direct cost. Tehran gains a layer of protection that is difficult for the U.S. or European agencies to dismantle quickly, while Moscow avoids the political blowback of openly providing state infrastructure. Second, the model creates a self-sustaining commercial revenue stream that also functions as strategic infrastructure. The provider can legitimately claim it is simply offering cybersecurity services to paying customers, yet the net effect is the protection of actors who advance shared anti-Western objectives. Third, it normalizes the existence of “bulletproof” services within the global internet, gradually eroding the ability of Western defenders to enforce norms around acceptable hosting practices.
This is not isolated to one provider or one proxy relationship. Public reporting shows similar patterns with other state-linked or criminal ecosystems that benefit from Russian jurisdiction: ransomware leak sites, phishing-as-a-service platforms, and hacktivist campaigns that blend data exfiltration with propaganda. In each case, the infrastructure enables continuity after takedowns, allowing the actors to rotate domains, maintain Telegram channels, and sustain pressure on targets ranging from critical infrastructure operators to individual journalists and dissidents.

The strategic value lies in the asymmetry. For Russia, weakened in conventional terms, these commercial nodes function as low-cost, high-resilience platforms that can be leveraged by proxies without crossing the threshold of direct state attribution. For the proxy (in this case an Iranian MOIS-linked persona), the arrangement provides operational sanctuary and the ability to project power globally while maintaining the fiction of independent “hacktivist” activity. The result is a hybrid-warfare toolkit that is both scalable and sustainable: Russia supplies the protective layer, the proxy supplies the operational labor and plausible deniability, and the West absorbs the cumulative costs in the form of disrupted supply chains, leaked sensitive data, and psychological operations aimed at domestic audiences.
Critically, this infrastructure also feeds directly into reflexive-control operations. By protecting the platforms that release timed leaks or disinformation, Russia and its partners can shape the information environment in ways that influence policy debates, amplify societal divisions, and erode trust in institutions. A leaked dataset published behind protected infrastructure does not merely embarrass a target — it can be weaponized to trigger media cycles, legal investigations, or public outrage that distracts decision-makers or pressures governments to alter support for Ukraine or other policies.
Western observers have long noted this dual-use pattern, yet responses remain fragmented. Sanctions on specific providers have been limited, and de-peering efforts are complicated by the global nature of internet routing. The providers themselves continue to operate openly, citing legitimate clients alongside the more problematic ones. This creates a persistent gray zone where commercial activity and state-enabled proxy operations blur together, making attribution and disruption politically and technically challenging.
In essence, dual-use cyber infrastructure transforms a conventional weakness (Russia’s inability to project large-scale military power) into a strategic advantage: the ability to wage sustained, deniable, and low-cost confrontation through proxies. It allows Moscow to maintain pressure on the West indefinitely, even while its conventional forces are tied down in Ukraine. The Handala case is not an anomaly but a visible demonstration of how this model functions in practice — providing resilience to aligned actors, enabling asymmetric operations, and contributing to the broader shadow-war campaign that defines today’s confrontation. As long as such infrastructure remains available and relatively unhindered, the proxy layer will remain a central pillar of Russia’s long-term hybrid strategy.
The Underestimated Long-Term Destructive Threat Landscape
The true danger of Russia’s shadow war lies not in the possibility of sudden kinetic escalation but in the slow, asymmetric corrosion it produces over years. Dual-use cyber infrastructure — the commercial providers that offer resilience to proxies — serves as the quiet backbone of this campaign. It allows Russia and its aligned actors to operate with persistence and deniability, turning conventional weakness into a strategic advantage that imposes cumulative harm on Western societies without ever crossing the threshold of open war.
At the operational level, these providers enable proxies to maintain continuity that would otherwise be impossible. When Western law-enforcement seizes domains or disrupts hosting, the actors simply migrate to infrastructure that sits under Russian jurisdiction and benefits from high-capacity scrubbing and anycast routing. The result is a resilient platform for leak-and-extortion operations, data exfiltration, and psychological campaigns. A state-linked proxy — such as an Iranian MOIS-affiliated group conducting high-profile compromises against U.S. and allied targets — can continue publishing stolen data, issuing threats, and claiming symbolic victories even after repeated takedowns. This resilience is not accidental; it is the product of a deliberate ecosystem that protects the flow of information while shielding the operators from swift disruption.
This infrastructure becomes especially potent when fused with reflexive control. By protecting the platforms that release carefully timed leaks or disinformation, Russia and its proxies create feedback loops that influence Western decision-making. A leaked dataset is not merely embarrassing; it is weaponized to trigger media cycles, congressional hearings, public outrage, or policy shifts. Narratives are seeded that portray Western support for Ukraine as reckless, or that amplify existing societal fractures. Over time, reflexive control aims to make democratic governments and publics reach conclusions that serve the adversary’s interests — all while believing those conclusions are their own. The protected infrastructure ensures the information keeps flowing even when platforms are taken down elsewhere.

The long-term destructive effects are subtle, cumulative, and chronically underestimated. Western security discourse tends to focus on high-visibility incidents: large-scale DDoS attacks, destructive malware, or headline-grabbing breaches. Yet the real damage often unfolds in slower, societal dimensions:
Indirect human costs: Ransomware operations against hospitals or supply-chain providers can delay critical care, leading to measurable increases in mortality. Data leaks enable targeted harassment, identity theft, or even real-world violence against individuals. Over years, these effects compound into tangible loss of life and public health without a single shot being fired.
Erosion of trust and cohesion: Repeated, protected information operations deepen polarization. Citizens lose confidence in institutions, media, and democratic processes. Studies of hybrid campaigns show measurable impacts on electoral turnout, policy support, and social trust. Reflexive control exploits these fractures, making societies less resilient to external pressure.
A concrete recent illustration of this dynamic is the Russian-linked disinformation campaign targeting France’s 2026 municipal elections. In the weeks leading up to local votes, coordinated networks created and amplified fake websites impersonating legitimate candidates and media outlets. One prominent case involved a fabricated site mimicking Paris mayoral candidate Pierre-Yves Bournazel’s campaign, falsely claiming he planned to convert the Centre Pompidou museum into housing for migrants. The story was rapidly spread through proxy channels and social media, exploiting existing societal fractures over immigration.
Although the original reporting was quickly debunked, the protected platforms ensured the narrative continued circulating even after initial takedowns. The operation deepened polarization, fueled public outrage against mainstream candidates, and eroded confidence in both political institutions and the electoral process itself. Many who amplified the story believed they were simply highlighting “real concerns” about migration policy — a classic reflexive-control outcome. Studies of similar hybrid campaigns show these tactics measurably reduce trust in democratic processes and can suppress electoral turnout or shift policy support in ways that benefit the adversary.
This example fits seamlessly after the sentence “Narratives are seeded that portray Western support for Ukraine as reckless, or that amplify existing societal fractures.”
https://www.newsguardrealitycheck.com/p/russia-has-its-eyes-on-paris

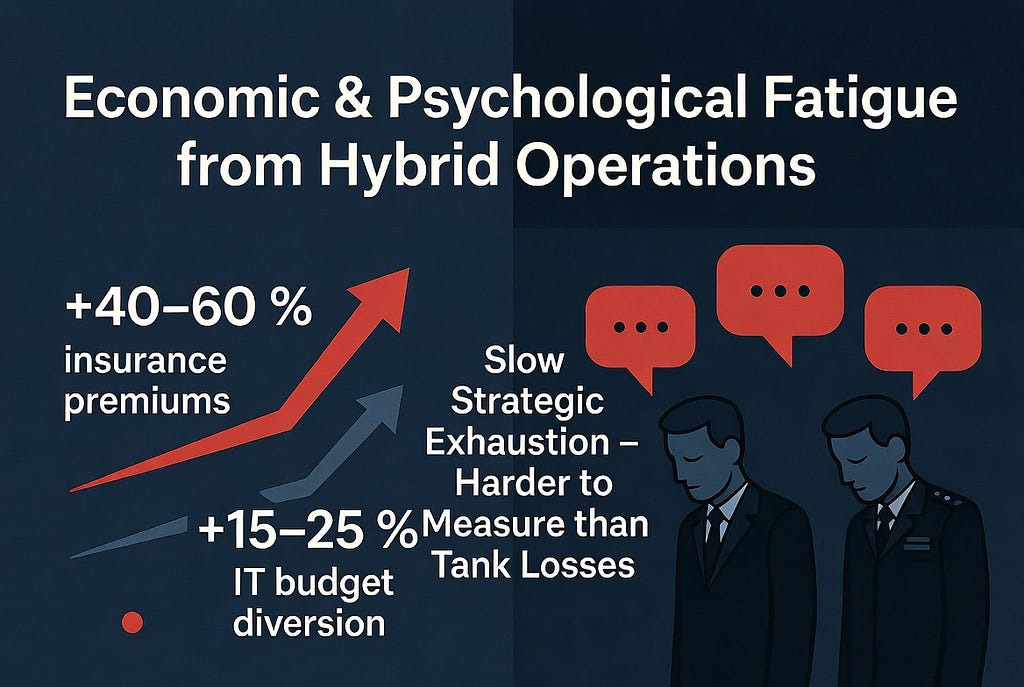
Economic and psychological fatigue: Each successful proxy operation raises defense, insurance, and resilience costs. Companies divert resources from innovation to cybersecurity; governments must constantly reassure publics after leaks or disruptions. The cumulative effect is strategic exhaustion a slow drain on national will and resources that is far harder to measure than tank losses or missile strikes.
A concrete recent example of this economic and psychological fatigue is the March 2026 warning from major European insurers (Allianz, AXA, and others) that cyber insurance premiums for critical infrastructure and healthcare had risen 40–60 % in the previous 12 months. The increase was driven by repeated ransomware and data-leak operations conducted by groups using Russian-protected infrastructure. Companies reported diverting 15–25 % of their IT budgets from innovation projects to cybersecurity resilience measures. At the same time, governments in France and Germany had to issue multiple public reassurance statements to calm citizens after high-profile hospital disruptions and leaks. The cumulative effect is a slow strategic exhaustion — a measurable drain on national resources and political will that is far harder to quantify than battlefield losses.
This threat landscape is underestimated for several structural reasons. First, it operates in the gray zone between cyber and information warfare, where attribution is slow and legal responses are cumbersome. Second, the damage is diffuse and long-term rather than immediate and spectacular; it does not produce the clear “before and after” images that drive policy. Third, Western strategic culture still prioritizes conventional and high-end cyber threats, often treating societal corrosion as a secondary or “soft” issue. The result is a persistent blind spot: the very tools that allow Russia to wage war indefinitely are precisely the ones that receive the least sustained attention and resourcing.
The proxy dimension amplifies this asymmetry. Russia does not need to conduct every operation itself. By providing protective infrastructure to aligned actors, it gains reach and deniability while the proxy absorbs the operational risk. The arrangement is self-reinforcing: successful operations generate revenue for the infrastructure providers, which in turn sustains the ecosystem. Over time, this creates a self-sustaining engine of confrontation that can run indefinitely, even as Russia’s conventional forces remain tied down in Ukraine.
The societal impact is not theoretical. Public reporting on state-linked leak campaigns shows how protected platforms contribute to real-world disruption of critical sectors, psychological operations aimed at domestic audiences, and the gradual normalization of hybrid interference as “just the way the internet works.” What appears as isolated incidents is, in reality, a coherent campaign of attrition waged against the fabric of open societies.
This is the destructive long-term threat landscape Russia has chosen. Unable to win quickly through conventional means, Moscow has bet on persistence, proxy enablement, and reflexive control to erode the West from within. The dual-use infrastructure that makes this possible is not a temporary workaround; it is a structural feature of the confrontation phase we now inhabit. Understanding this layer — and recognizing how profoundly it is underestimated — is essential to crafting effective responses. The next section examines what those responses could look like.
Western Counters and Strategic Implications
The long-term destructive threat landscape created by Russia’s dual-use cyber infrastructure and proxy-enabled reflexive control is real and persistent, but it is not insurmountable. The West possesses significant advantages in technology, alliances, economic leverage, and societal resilience — provided it shifts from a reactive posture to a proactive, sustained strategy that raises the cost of gray-zone operations without triggering unwanted escalation.
The most immediate tactical counters focus on disrupting the resilience that dual-use providers offer to proxies. De-peering abusive infrastructure at the global routing level has proven effective in past cases: when major Western carriers and CDNs systematically drop traffic from known bulletproof networks, the operational tempo of protected actors slows dramatically. Targeted sanctions on the commercial entities themselves — or on the financial and technical intermediaries that support them — can further constrain their business model. Because these providers rely on international peering and payment systems to remain profitable, coordinated action by the U.S., EU, and key Asian partners can shrink the safe operating space without direct military involvement.
At the same time, Western governments and the private sector must accelerate resilience standards across critical sectors. Mandatory minimum cybersecurity requirements for hospitals, energy operators, and supply-chain companies — combined with incentives for rapid adoption of diversified hosting and advanced behavioral filtering — reduce the payoff of proxy ransomware or leak operations. Intelligence sharing between NATO, the EU, and Five Eyes partners has already improved dramatically since 2022; expanding real-time telemetry exchange to include commercial providers and smaller allies would close many of the attribution gaps that currently favor the attacker.
Medium-term systemic responses must address the reflexive-control layer head-on. Democratic societies need better tools to detect and counter coordinated information operations that exploit protected platforms. This includes transparent labeling of state-linked leak campaigns, investment in independent fact-checking ecosystems, and public education on how reflexive control manipulates decision-making. Regulatory pressure on social-media platforms to improve moderation of timed, proxy-sourced narratives can blunt the societal corrosion without compromising free speech. The goal is not to win an information war but to make reflexive control less effective by increasing the “friction” that adversaries must overcome.
Strategically, the West must accept that this confrontation is the new normal. Russia’s conventional weakness makes hybrid and proxy tools more attractive, not less. The correct response is therefore calibrated persistence: maintain strong conventional deterrence on NATO’s eastern flank while steadily increasing the price of gray-zone activity. This includes sustained support for Ukraine — not as charity, but as a forward line of defense that keeps Russian forces tied down and prevents the shadow war from expanding. Economic statecraft (targeted sanctions, export controls on dual-use technologies) and diplomatic pressure on third countries that host enabling infrastructure will remain essential.
Importantly, these counters must be designed to avoid escalation ladders that Russia could exploit for domestic propaganda. Over-militarization of the cyber domain or overly aggressive de-platforming campaigns risk feeding Kremlin narratives of “Western aggression.” The smarter path is quiet, multilateral, and rules-based pressure that leverages the West’s collective economic and technological superiority.
The broader implication is clear: victory in this prolonged confrontation will not be measured in battlefield breakthroughs but in societal endurance and institutional adaptability. Russia bets that Western publics and governments will eventually tire of the constant low-level attrition. The West’s counter-bet must be that open societies, when properly informed and hardened, possess greater long-term resilience than authoritarian systems built on coercion and denial.
By treating dual-use infrastructure and proxy-enabled reflexive control as the central pillars of Russia’s strategy — rather than peripheral annoyances — the West can move from defense to strategic competition. The tools exist. The question is whether the political will and sustained focus will match the threat. In a confrontation that rewards persistence over spectacle, the side that best protects its societal cohesion while raising the cost of the adversary’s gray-zone playbook will ultimately prevail.
Conclusion
Russia’s conventional weakness in Ukraine has not produced de-escalation. It has instead forged a new and more durable form of confrontation — a prolonged shadow war in which dual-use cyber infrastructure, proxy actors, and reflexive control serve as the primary instruments of pressure. The repeated migration of Iranian state-linked groups such as Handala to Russian-protected providers is not an isolated technical footnote; it is a visible demonstration of how Moscow transforms commercial resilience into strategic advantage. By shielding proxies, Russia extends its reach at minimal cost, maintains plausible deniability, and imposes cumulative harm on Western societies without ever crossing the threshold of open armed conflict.
This is the destructive long-term threat landscape that defines today’s confrontation. Reflexive control and protected information operations erode public trust, deepen polarization, and shape policy debates in ways that appear organic to the target. The societal corrosion — measured in indirect casualties from disrupted hospitals and supply chains, in strategic fatigue, and in the gradual normalization of hybrid interference — is slower and subtler than missile strikes or tank battles. Yet over years it can prove more corrosive to open societies than any single kinetic event. Western analysis has too often treated these tools as peripheral or “soft” threats. In reality, they are central to Russia’s strategy precisely because its conventional forces are depleted and its economy is under sanctions stress.
The confrontation we now inhabit is therefore neither temporary nor easily resolved. It is the new normal of great-power competition in an era when nuclear deterrence and mutual conventional exhaustion make direct war prohibitively expensive. Russia has chosen the gray zone because it plays to its remaining strengths: tolerance for prolonged pain, control over domestic narratives, and the ability to operate outside Western rules.
For the West, the path forward is demanding but achievable. Success will come not from spectacular countermeasures but from consistent, patient resilience: systematically raising the cost of proxy enablement through coordinated de-peering, targeted sanctions, and hardened critical infrastructure; countering reflexive control with transparent information practices and societal education; and maintaining strong conventional deterrence while supporting Ukraine as the forward line of the broader contest. Open societies have historically demonstrated remarkable endurance when they understand the nature of the threat and respond with clarity and unity.
The ultimate outcome of this long contest will be decided less by who can inflict the most immediate damage and more by who can better preserve cohesion, adaptability, and will over time. Recognizing dual-use infrastructure and proxy-enabled reflexive control as central — rather than peripheral — to Russia’s strategy is the essential first step.
How Russia’s Dual-Use Cyber Infrastructure Fuels a Destructive Shadow War was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.
