It Didn’t Look Dangerous at First
Every SOC analyst knows this feeling.
You’re watching dashboards.
Logs are flowing.
Nothing critical. Nothing red.
Then you notice one IP address.
It’s not triggering a high-severity alert.
It’s not exploiting anything.
It’s just persistent.
50–100 requests per second.
Not a spike.
Sustained.
That’s when instinct kicks in.
Introduction:- When “Google LLC” Doesn’t Mean Safe
In security operations, not every investigation starts with a loud alert. Sometimes it begins with something subtle, a pattern that doesn’t feel right.
During routine monitoring, we noticed a sustained spike in traffic from a single IP address. It wasn’t triggering exploit signatures. It wasn’t causing application crashes. But it was consistently generating between 50–100 HTTP requests per second.
At first glance, the source appeared harmless. The ISP was listed as Google LLC. For many teams, that would immediately reduce suspicion. After all, Google’s infrastructure is trusted, widely used, and often associated with legitimate services like Googlebot or Google Cloud APIs.
But reputation alone is not evidence of legitimacy.
That assumption is where many investigations fail.
Phase 1:- Identifying the Traffic Pattern
The first step was to analyze the raw web logs. Instead of normal user navigation, we observed direct endpoint requests with highly structured patterns:
/a
/aa
/ab
/admin
/backup
/config
/.env
This behavior did not resemble human browsing. There were no CSS requests, no image loads, no JavaScript assets, and no sequential page navigation. Instead, the requests targeted potential sensitive endpoints directly.
One path in particular stood out: /.env.
In modern web applications, .env Files often store environment configuration data, such as:
- Database credentials
- API tokens
- SMTP configuration
- Encryption secrets
If exposed due to misconfiguration, this file alone can lead to full system compromise.
The server returned HTTP 400 for this request, which indicated no exposure. However, the intent behind the request was clear: this was reconnaissance.
Phase 2:- Verifying the Source Infrastructure
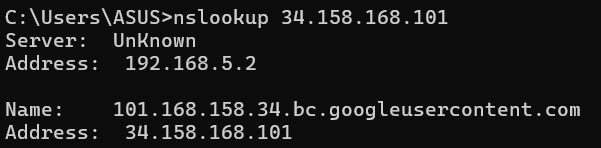
To better understand the origin of the traffic, we performed a reverse DNS lookup:

This was a critical discovery.
The IP was not associated with Googlebot. It was not a crawler IP resolving to googlebot.com. Instead, it resolved to a googleusercontent.com domain, a strong indicator of Google Cloud Compute Engine infrastructure.
This meant the traffic originated from a rented virtual machine inside Google Cloud.
In other words, the infrastructure belonged to Google, but the activity did not.
Why Cloud Infrastructure Is Commonly Used for Reconnaissance
Modern attackers rarely operate from suspicious home networks. They leverage public cloud platforms because cloud environments provide:
- Clean IP reputation
- High bandwidth
- Easy deployment and teardown
- Scalability
- Global distribution
More importantly, cloud ASN ranges are massive. Blocking an entire Google ASN (such as AS15169 or related allocations) would disrupt legitimate services. That makes cloud-hosted reconnaissance difficult to mitigate using simple IP blocking strategies.
Phase 3:- Behavioral Analysis vs. User-Agent Trust
The HTTP headers showed a completely normal User-Agent string:
Mozilla/5.0 (Windows NT 10.0; Win64; x64) Chrome/120.0
If analysis stopped at this point, the traffic might have been dismissed as legitimate.
However, deeper behavioral analysis revealed:
- No static asset retrieval
- No session cookie reuse
- No referrer chain
- No realistic timing gaps
- Sequential endpoint probing
- Sustained high request rate
User-Agent strings are trivial to spoof. A single line of code in Python, Go, or curl can replicate any browser signature. Behavioral patterns, however, are far more difficult to fake convincingly.
The mismatch between declared identity (browser) and actual behavior (automated probing) confirmed the activity was scripted.
Phase 4: Cross-System Correlation
While investigating web logs, we correlated events across additional security layers. On the F5 BIG-IP VPN appliance, we observed repeated entries:
tmm: ssl handshake failed
The VPN portal was publicly accessible, meaning external systems could attempt TLS negotiations freely. SSL handshake failures in this context may indicate:
- TLS version probing
- Cipher suite fingerprinting
- Malformed ClientHello packets
- Automated vulnerability scanning tools
When timestamps were aligned, we observed overlap between:
- Web application enumeration
- VPN handshake failures
- Google Cloud–based IP ranges
This suggested infrastructure mapping activity rather than isolated web probing.
Classification: Reconnaissance, Not Exploitation
At this point, we did not observe:
- Successful authentication
- SQL injection payloads
- Credential brute-force attempts
- Data exfiltration
- Exposed sensitive files
However, this activity aligns strongly with MITRE ATT&CK Technique T1595 Active Scanning.
Reconnaissance is often the quietest phase of an attack lifecycle. It is the phase where adversaries map exposed surfaces, measure response behavior, and test configuration weaknesses before attempting exploitation.
Detecting reconnaissance early reduces downstream risk significantly.
Why IP Blocking Alone Is Insufficient
Blocking the identified IP would have been simple. However, cloud infrastructure allows near-instant redeployment. An attacker can destroy a virtual machine and launch another in minutes, often within the same IP range.
Instead of relying solely on IP-based mitigation, we implemented behavior-based controls:
- Rate limiting for abnormal request bursts
- WAF rules blocking direct access to sensitive files
- Alerts for high 404 response ratios
Key Lessons from This Investigation
- User-Agent strings cannot be trusted alone.
- Cloud-hosted reconnaissance is increasingly common.
- Early detection of reconnaissance improves overall security posture.
- Behavior-based detection outperforms reputation-based filtering.
The most important takeaway is simple: modern attacks do not originate from obviously malicious networks. They originate from trusted platforms used legitimately by millions of organizations worldwide.
Real Investigation:- How We Traced Google Cloud IP Recon Activity was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.