
As cybercrime in Brazil continues to grow in sophistication, a group known as “Tropa do Arraca” has emerged as a notable threat actor. The group is reportedly involved in stealing mobile devices and then using phishing kits to extract additional digital assets from victims. In this article, we leverage OSINT (Open Source Intelligence) investigation and analysis through the threat hunting platform Criminal IP to examine the group’s infrastructure and malicious operational management, uncovering their complex tactics. We also focus on analyzing specific phishing kits, particularly those targeting iCloud credentials, to understand the group’s level of sophistication better.
Where the Inquiry Begins: Suspicious Signatures and a Phishing Operation
The analysis and investigation into “Tropa do Arraca” began with what appeared to be a seemingly ordinary fragment of HTML code. However, upon closer inspection, the code was revealed to be a phishing kit meticulously designed to mimic the iCloud login page.
Within the analyzed source code, the following hidden fields were identified:
<input id=”AppleAccount” type=”hidden” value=”kittropadoarranc_Tropa”/>

The string “kittropadoarranc_Tropa” found within the field was not a simple error or random identifier. It functioned as a digital signature pointing to “Tropa do Arraca,” suggesting a group already known within Brazil’s cybercrime ecosystem. From this point onward, the investigation expanded beyond the analysis of a single phishing kit into a broader effort to track an organized threat group.
Inside “Tropa do Arranca”: Reflecting Brazil’s Evolving Cybercrime Scene
The term “arranca” in Brazilian slang refers to forcefully or swiftly taking something away. In the context of cybercrime, “Tropa do Arranca” appears to specialize not only in the physical theft of mobile devices, but also in extracting victims’ digital access, particularly iCloud account credentials.
Their ultimate objectives include:
- Unlocking stolen or lost Apple devices
- Reselling devices on illicit markets
- Gaining access to banking information and other sensitive data
The investigation revealed that the group operates on platforms such as Telegram, managing multiple channels used to coordinate criminal activities and trade illicit services.
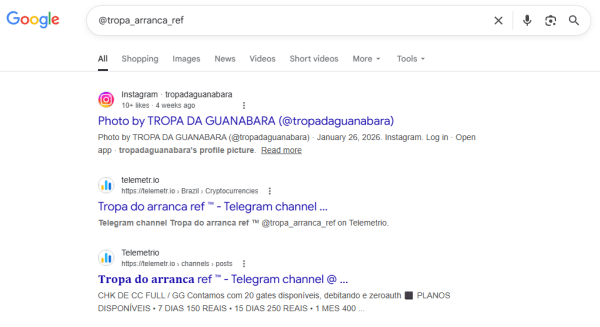
Example channels:
- @ghostreff (focused on BIN checking and data lookup)
- @tropa_arranca_ref (sharing scam success cases and references)
Crafting Credibility: Social Engineering and Location-Based Deception in Phishing Schemes

The phishing kit attributed to this group appears to be carefully designed to exploit victim psychology. While mimicking Apple’s “Find My” interface, it incorporates specific geographic coordinates, including:
- -23.5557714
- -46.6395571
These coordinates correspond to a real-world location near the Jacequai Viaduct and Avenida 23 de Maio in central São Paulo, Brazil.
The phishing structure leveraging location data goes beyond simple UI replication. While typical phishing pages are designed primarily around login input fields, this case inserts real geographic coordinates to induce cognitive trust in the victim.
Especially, the design targets the psychological instability immediately following device theft and exhibits the following characteristics:
- Imitation of a legitimate map API structure
- Display of coordinate-based location markers
- Staged “device found” messaging
- Prompts demanding immediate action
By replicating a legitimate interface and embedding precise geographic coordinates, this strategy reinforces a sense of authenticity. In situations where victims are desperate to recover a stolen device, seeing an exact location displayed on a map increases their belief that the device is genuinely being tracked. This heightened urgency significantly raises the likelihood that victims will enter their iCloud credentials, ultimately handing over account access directly to the attackers.
This is not an exploitation of a technical vulnerability, but rather a location-based social engineering strategy designed to manufacture trust.
Analyzing Malicious Infrastructure with Criminal IP

Criminal IP Domain Search: icoudbuscar[.]net
The investigation was further expanded to map the digital infrastructure associated with “Tropa do Arranca” using Criminal IP. Through Domain Search, multiple malicious domains and compromised IP addresses were identified, all of which carried high risk scores. One of the domains uncovered during analysis, icloudbuscar[.]net, was rated at a “Critical” risk level and assessed as highly likely to be a phishing domain.
In addition to the domain identified above, a total of 10 connected domains were confirmed, including the following examples. Most of these domains were recently registered, indicating that the group is rapidly establishing and operating new infrastructure to sustain its activities.
- icloudbrasil[.]net
- applerastreio[.]net
- rastreioapple[.]net
- icloudseguro[.]com
Connected IP Address Analysis
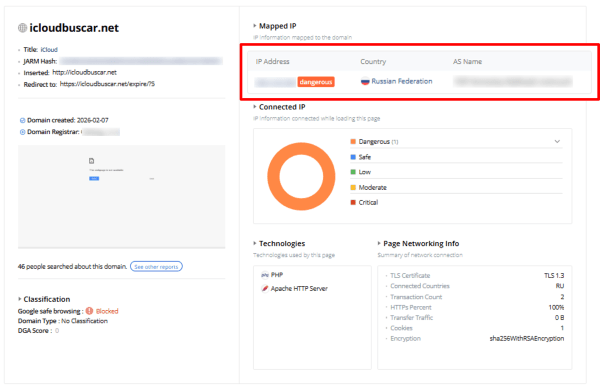
A specific IP address confirmed to be connected to the group’s infrastructure through Criminal IP Domain Search was further analyzed using Criminal IP Asset Search.

Criminal IP Asset Search Results:
- Inbound Risk Score — Critical
- Outbound Risk Score — Dangerous
The fact that the Inbound risk score is rated Critical and the Outbound risk score Dangerous indicates that the IP is not merely hosting a phishing page, but is actively involved in malicious inbound traffic and outbound communications. This can be interpreted as a quantitative indicator that the IP is highly likely being used as part of an attack infrastructure. The IP address was confirmed to be located in Russia and was associated with multiple domains. The presence of several domains mapped to the same IP suggests that this is not a single phishing site operation, but rather part of a multi-domain campaign infrastructure.
Risk Mitigation and Actionable Insights
This case demonstrates a multi-stage attack structure that extends beyond a simple phishing site, combining physical device theft with subsequent digital credential theft. Therefore, proactive measures are required from both users and security teams.
Protective Guidelines for End Users
- Do not enter iCloud credentials into links received via SMS, messaging apps, or email after device theft.
- Access Apple’s official website directly to verify account status.
- Enable multi-factor authentication and keep recovery email/phone information up to date.
- Report stolen devices through official carrier or manufacturer channels.
Strategic Recommendations for Organizations and Security Teams
- Continuously monitor newly registered domains containing brand-related keywords such as “Apple,” “iCloud,” or “rastreio.”
- Apply detection policies combining recently registered domains (within 30 days) and high Domain Scoring.
- Track multi-domain hosting infrastructures based on foreign IP addresses.
- Accumulate and analyze phishing kit HTML patterns and obfuscated malicious scripts.
- Conduct OSINT monitoring of Telegram-based criminal channels.
By implementing these recommendations, organizations can move beyond blocking individual phishing sites and establish a proactive defense system that addresses associated infrastructure. Early identification of newly registered brand-abusing domains and high-risk IP addresses is critical to stopping attacks before victimization occurs. Continuous external asset monitoring combined with threat intelligence–driven analysis is essential.
Conclusion
Although “Tropa do Arranca” is not officially classified as a global threat group, the phishing kit and infrastructure patterns identified in this case exhibit clear signs of an organized campaign.
Notable characteristics include:
- The combination of physical device theft and digital credential theft
- Trust-inducing social engineering using real geographic coordinates
- Rapid creation of multiple brand-abusing domains
- Multi-domain hosting infrastructure based on foreign IP addresses
- Fast domain rotation strategies
These findings demonstrate that a single-site blocking approach is insufficient. Instead, organizations must adopt an attack surface management–oriented strategy that continuously monitors externally exposed assets. Newly registered domains and high-risk IP addresses should be identified before an attack occurs, not after victimization.
In relation to this, you can refer to RedNovember and APT40 Activity in the Pacific: Observations by Criminal IP
This article is based on an analysis shared by the Twitter-based threat intelligence specialist, Clandestine.
Mapping the Digital Network of “Tropa do Arranca”: Inside a Brazilian Phishing Kit was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.
